Definition of Proxy Server in The Network Encyclopedia.
What is Proxy Server?
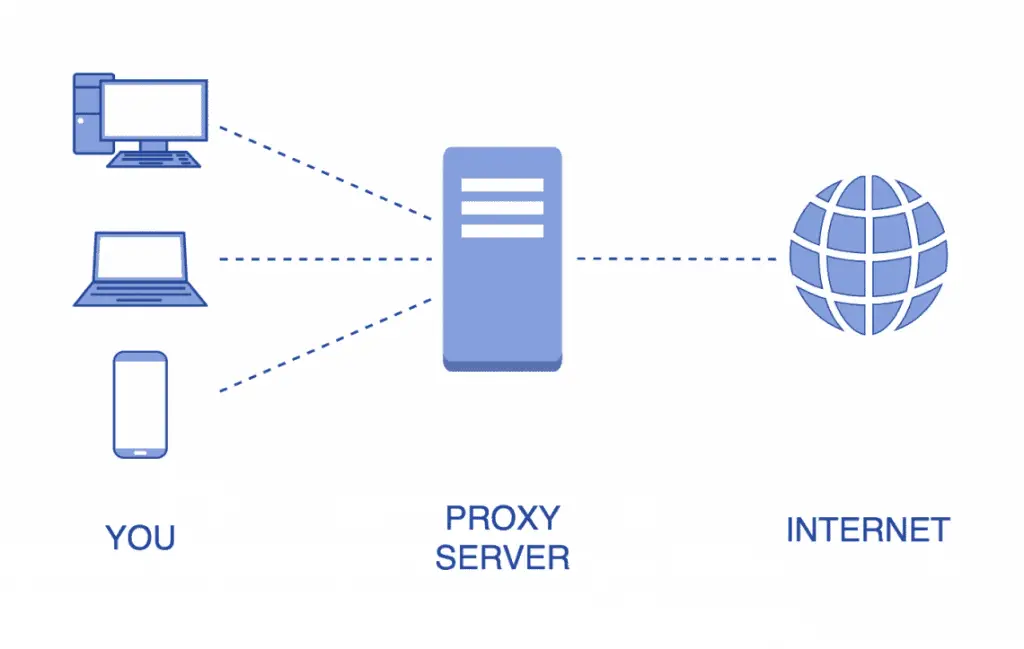
A Proxy Server is a computer or network device that can act on the behalf of other computers to request content from the Internet or an intranet.
How Proxy Server Work?
Proxy servers act as secure gateways to the Internet for client computers. They are transparent to client computers – a user interacting with the Internet through a proxy server is not aware that a proxy server is handling the requests unless the user tries to access a resource that the proxy server is configured to disallow. Similarly, the Web server receiving the requests from the proxy server interprets these requests as though they came directly from client computers.
Proxy servers can be used to secure private networks connected to unsecured public networks such as the Internet. They have greater functionality than packet-filtering routers because they operate at a higher level of the protocol stack and afford greater control over monitoring and managing network access. A proxy server functioning as a security agent for a private network is generally called a firewall.
Two types of proxy servers are used in network firewall environments:
- Circuit-level gateways
- Application-level gateways
Circuit-level gateways
Circuit-level gateways establish virtual circuits between machines on the internal private network and the proxy server on the border of the private network. The proxy server controls all connections between the internal private network and the external public network. If a client on the private network wants to access the Internet, for example, the Hypertext Transfer Protocol (HTTP) request packet generated by the client’s Web browser traverses the virtual circuit to the proxy server; the proxy server then changes the source IP address of the packet to that of the external (public) network interface of the proxy server and forwards the packet onto the Internet. When a remote HTTP server on the Internet sends a response, the proxy server routes this response back through the virtual circuit to the client that made the request. To learn more about Circuit-level gateways click here.
Application-level gateway
An application-level gateway can implement security policies for analyzing packets that reach the external (public) interface of the proxy server from distrusted public networks. These security policies can examine packet addresses and other header information, permit or deny packets on the basis of their contents, and modify the address, header, or contents of packets that they monitor in order to hide key information about the internal network’s applications and services. Application-level gateways provide proxy services only for specifically configured applications and protocols such as HTTP, File Transfer Protocol (FTP), Simple Mail Transfer Protocol (SMTP), and Telnet. For each type of application for which you want to regulate access through the firewall, you must install and configure a related proxy service on the proxy server. Applications and protocols for which a proxy service is not installed cannot be accessed through the firewall.
NOTE
Instead of using a proxy server, you can provide modems for and run telephone lines directly to each user who needs Internet access, but this option is costly. You can also configure a physically separate network with several computers that have shared Internet access, but this is cumbersome for users. Advantages of using a proxy server include the following:
- It provides a single, secure gateway to manage.
- It can provide different types of access to the Internet as appropriate for each group of users.
- It can monitor and track Internet usage for each user.
- Many users can share a single high-speed Internet connection.
Microsoft Proxy Server is an example of a proxy server and firewall product that provides a secure gateway for your network to the Internet.