Server Management Tools are a set of tools hosted in Azure and available for free with a new web-based graphic user interface. Learn how to easily use those tools.
As infrastructure and deployments become more hybrid in nature, where we have workloads spread across clouds, the management effort to control all these different areas increases exponentially. This is obviously a bad thing and we want to be able to provide a more controlled way to manage resources which might exist on-premises but also in Azure.
The next figure presents an overview of what a deployment with the server management tools would look like.

You will also observe from the diagram that a gateway server (in the middle of the diagram) is required to allow on-premises infrastructure to communicate with the service in Azure.
Server management tools (SMT) introduces a web-based GUI hosted in Azure and command-line tools that can do this for your Windows Server 2016 estate. For instance, your administrators can manage Nano Server or server core easily from this GUI without affecting the footprint of those deployments.
The tool currently has the following capabilities:
- View and change system configuration
- View performance across various resources and manage processes and services
- Manage devices attached to the server
- View event logs
- View the list of installed roles and features
- Use a Windows PowerShell console to manage and automate
SMT support for Windows 2012 and later
If this is a Windows 2016 Server, no prerequisite work is required, but if you are using a previous edition of Windows (i.e., 2012 or 2012 R2) you must install WMF 5.0 so that you can manage Windows Server 2016 hosts, including Nano Server.
With the exception of Windows Update and Device Manager, all SMT tools will work with Windows 2012 and 2012 R2. There is one thing to consider when approaching SMT and using it to manage your previous versions of Windows: the dependencies of installed applications on the server. For example, will your application break if you install a newer version of WMF?
Persistent credentials
In Windows Server 2016 Server Management Tools, you can store credentials encrypted by using AES256 encryption and stored in Azure. The gateway is responsible for encrypting these credentials with a certificate that only exists on the gateway before uploading the credentials to Azure in a secured state. These credentials can then be decrypted only by the gateway using the certificate that encrypted the credentials in the first place. The certificate, as stated, never leaves the gateway and only ever exists on the gateway.
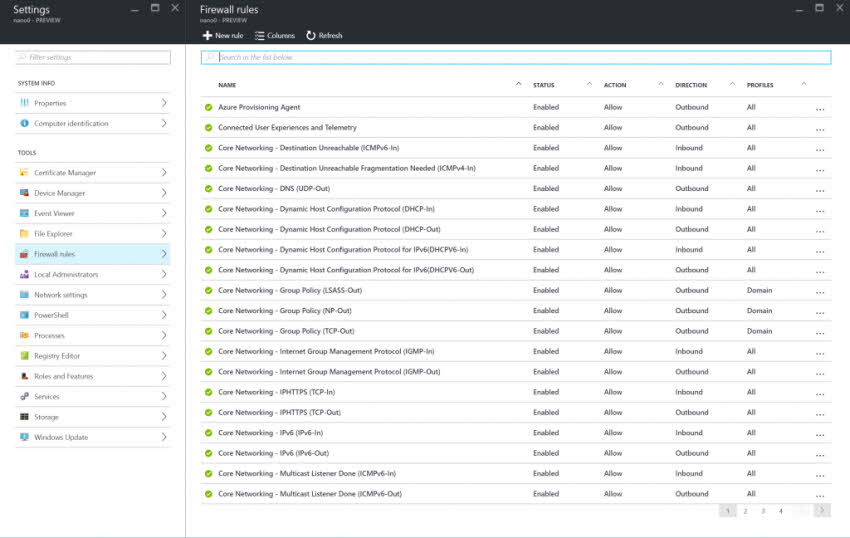
Firewall rules
Centrally managing a Windows firewall provides numerous benefits to servers by ensuring that a standardized policy is enforced. Unfortunately, dealing with a Windows firewall outside of traditional enterprise monitoring tools typically has been a difficult task; you can’t easily work at scale and it can be difficult to gather a complete understanding of what rules are turned on and what their status is. In SMT, Microsoft provides GUI support for looking at the firewall rules on a specific machine, making it easier to understand what is happening, as demonstrated in the next figure.
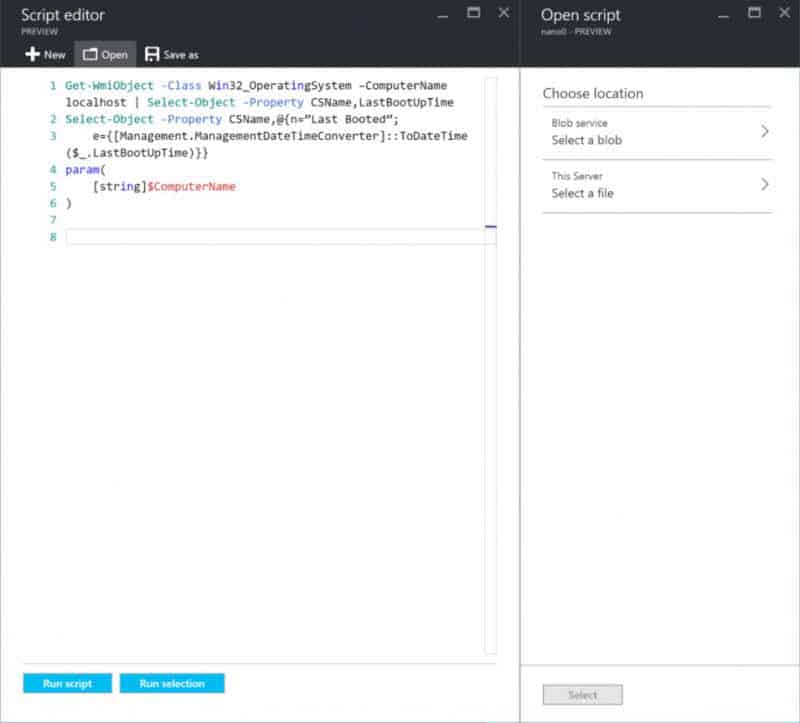
Windows Power Shell script editor enhancements
The Windows PowerShell script editor in SMT has been upgraded to support file-browsing capabilities on a machine. Now, you can open, edit, and save scripts on specified machines.
The script editor also has the ability to connect directly to an Azure Storage Blob (see Figure 5-28) and save your scripts to it. The scripts then become accessible to all servers in your subscription and beyond.
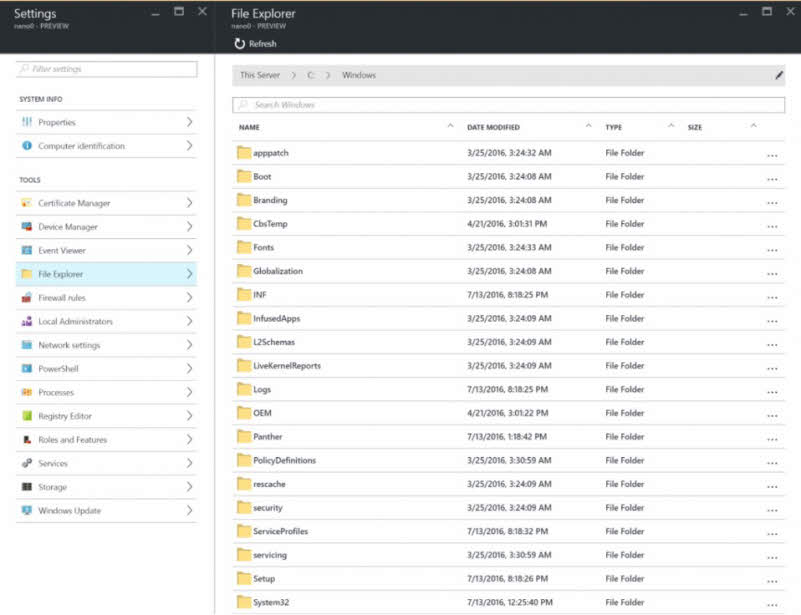
File Explorer
Along with the Windows PowerShell script editor’s basic capabilities to interact and work with scripts on specified machines, you also can perform basic file management activities like browse, rename, and delete. The next figure shows you a sample of what File Explorer in SMT looks like.
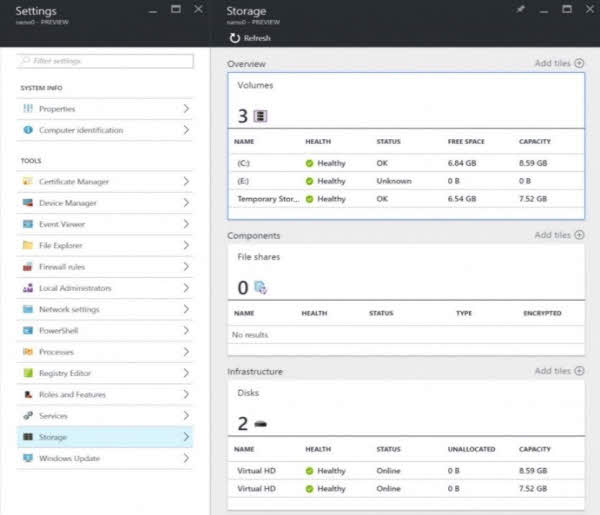
Local Storage
SMT now has the ability to provide more detailed info on storage for a specific machine. You can display information about drives, volumes, and file shares. Currently, that information is available in a read-only format, but this technology will evolve over time. The next figure demonstrates this capability.
Certificate Manager
Certificates for any IT organization presents challenges in terms of its management; for example, how do you verify certificates across multiple machines if you don’t run a Certificate Authority. SMT introduces a certificate manager so you can now remotely manage certificates on specified machines. The next figure shows how you now can view all or a scoped set of certificates, look at the event log, and manage certificate lifecycles with import, export, and delete functions.
Deployment
Deployment of SMT is relatively straightforward; however, it does involve the use of Azure and will require an Azure subscription. There are various ways of obtaining an Azure subscription but the simplest is to go to https://azure.microsoft.com/free/. Here, you can create a subscription if your organization does not already have one.
The gateway server you will create also needs Internet access, so it will need to be on a routable subnet within your organization.
External References
For all the latest information about Server Management Tools for Windows Server read:
- Deploy Server Management Tools with GUI (Graphic User Interface)
- Deploy Server Management Tools with PowerShell
- Further reading on Windows Server Management (Blog Technet)
- Prepare for the MTA 98-365 exam: Windows Server 2016 Administration Fundamentals from Amazon
- Learn more with this top rated book: Windows Server 2016 Inside Out by Orin Thomas from Amazon
How to setup Server Management Tools in Azure
Learn about this new web-based GUI management tool that is hosted in Azure and available for no charge. Especially useful when managing headless servers such as Nano Server and Server Core, it can be used to manage on-premises infrastructure alongside Azure resources.