Definition of SOCKS v5 in Network Encyclopedia.
What is SOCKS v5?
SOCKS v5 is a circuit-layer proxy protocol used in client/server networking environments. SOCKS lets hosts on each side of a proxy server communicate with each other by establishing a relay connection between the internal and external networks.
SOCKS also provides authentication functions for controlling access between networks. SOCKS is widely implemented in both proxy server and firewall software, especially for allowing hosts on a private network to access the Internet while preventing distrusted hosts on the Internet from accessing the private network. SOCKS v5 is defined in Request for Comments (RFC) 1928, 1929, and 1961.
How It Works
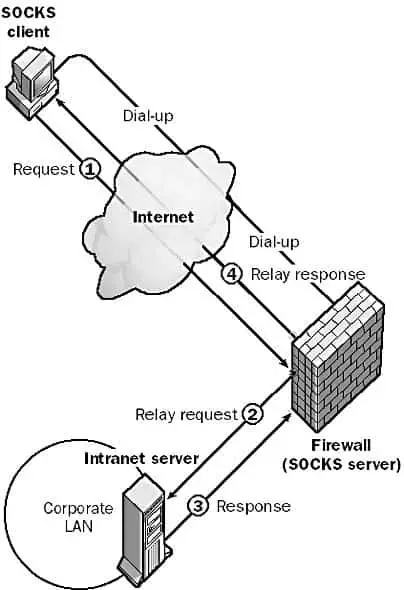
When a host on one side of a proxy server wants to connect to a host on the other side to access network resources, SOCKS server software running on the proxy server authenticates the host’s request, creates a circuit-level proxy connection to the target host, requests the necessary data, and relays the information back to the requesting host.
The SOCKS client on the requesting host first negotiates an authentication method with the SOCKS server, and then sends the user’s credentials to the SOCKS server for authentication.
SOCKS v5 supports a number of authentication methods, including Challenge Handshake Authentication Protocol (CHAP) and digital certificates. Once the user is authenticated, the SOCKS client sends a request message using the SOCKS protocol to the SOCKS server (the daemon or SOCKS service running on the proxy server). This request message contains the address of the target host, such as a Web server on a corporate intranet. The SOCKS server then establishes a Transmission Control Protocol (TCP) connection with the target host that functions as a proxy circuit between the requesting and target hosts. Once this “virtual circuit” is established, the SOCKS server notifies the SOCKS client and communication can begin between the two hosts, with the SOCKS server relaying each packet sent between them.
SOCKS also supports public-key encryption for secure, encrypted transmission of data.
The previous version of the protocol, SOCKS v4, was more difficult to configure on the client side and had no support for authentication of users or encryption of data. It also did not support User Datagram Protocol (UDP) traffic. SOCKS v5 is easier to configure, supports various authentication methods and encryption algorithms, and supports connectionless UDP traffic.
NOTE
To use SOCKS, you must have SOCKS-enabled client software installed on the hosts that will be communicating over the proxy server. Using SOCKS, virtual circuits are set up and torn down between the two hosts on a session-by-session basis. SOCKS servers usually include comprehensive logging functionality to analyze the flow of traffic between the trusted and distrusted networks.
TIP
To access Microsoft NetShow servers through a firewall, you must upgrade from SOCKS v4 to SOCKS v5 because NetShow uses UDP connectionless communication. Microsoft Proxy Server supports the SOCKS protocol and can act as a secure circuit-level gateway between a private network and a distrusted public network such as the Internet.